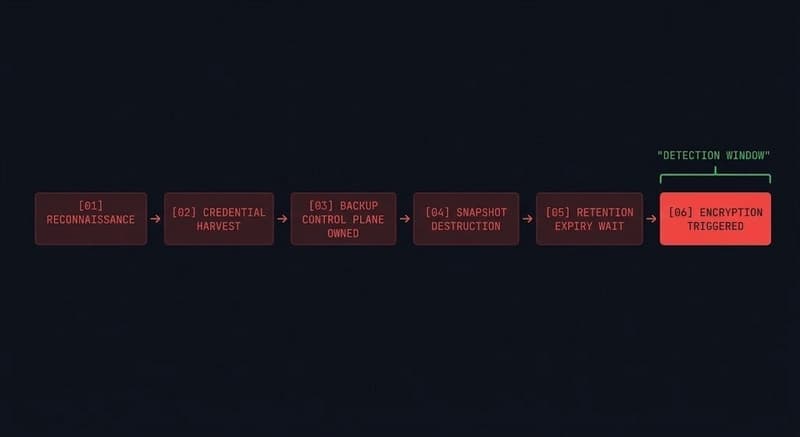
Ransomware backup architecture fails the moment you design it for accidental failure instead of adversarial intent. Assume the attacker has your runbooks. Not as a theoretical exercise — as an operational reality. Modern ransomware groups conduct reconnaissance that lasts weeks. They map your backup
⚡Key InsightsAI analyzing…
N
NTCTech
📡
Tags:#cloud#dev.to
Found this useful? Share it!
Read the Full Story
Continue reading on Dev.to
Related Stories
☁️
☁️Cloud & DevOps
Concurrency vs parallelism in Go: applied to Event Sourcing and CQRS
about 6 hours ago
☁️
☁️Cloud & DevOps
How Redis Caching Actually Works — A Visual Guide for Backend Developers
about 6 hours ago
☁️
☁️Cloud & DevOps
FaultRay: Why We Formalized Cascade Failure Propagation as a Labeled Transition System
about 6 hours ago
☁️
☁️Cloud & DevOps
GitHub Actions: Scoping environment variables across environments without wildcards
about 6 hours ago