24 stories
 Dark Reading
Dark ReadingFraud Rockets Higher in Mobile-First Latin America
Cyber-fraudsters move quickly from compromised devices to account takeover to funds transfer, shifting money before many financial institutions can react.
 Dark Reading
Dark ReadingFull Sail University to Open IBM Cyber Defense Range Powered by AWS and Cloud Range on Campus
 Dark Reading
Dark ReadingNiobium Introduces The Fog
 Dark Reading
Dark ReadingPluralsight Launches SecureReady to Help Organizations Build Job-Ready Cybersecurity Teams
 The Hacker News
The Hacker NewsAPT28 Deploys PRISMEX Malware in Campaign Targeting Ukraine and NATO Allies
The Russian threat actor known as APT28 (aka Forest Blizzard and Pawn Storm) has been linked to a fresh spear-phishing campaign targeting Ukraine and its allies to deploy a previously undocumented malware suite codenamed PRISMEX. "PRISMEX combines advanced steganography, component object model (COM)
 Dark Reading
Dark ReadingIranian Threat Actors Disrupt US Critical Infrastructure Via Exposed PLCs
Attackers compromised Internet-facing OT devices and caused file and display manipulation, operational disruption, and financial losses across sectors.
 The Hacker News
The Hacker NewsShrinking the IAM Attack Surface through Identity Visibility and Intelligence Platforms (IVIP)
The Fragmented State of Modern Enterprise Identity Enterprise IAM is approaching a breaking point. As organizations scale, identity becomes increasingly fragmented across thousands of applications, decentralized teams, machine identities, and autonomous systems. The result is Identity Dark Matter: i
 The Hacker News
The Hacker NewsAnthropic's Claude Mythos Finds Thousands of Zero-Day Flaws Across Major Systems
Artificial Intelligence (AI) company Anthropic announced a new cybersecurity initiative called Project Glasswing that will use a preview version of its new frontier model, Claude Mythos, to find and address security vulnerabilities. The model will be used by a small set of organizations, including A
 The Hacker News
The Hacker NewsN. Korean Hackers Spread 1,700 Malicious Packages Across npm, PyPI, Go, Rust
The North Korea-linked persistent campaign known as Contagious Interview has spread its tentacles by publishing malicious packages targeting the Go, Rust, and PHP ecosystems. "The threat actor's packages were designed to impersonate legitimate developer tooling [...], while quietly functioning as ma
 The Hacker News
The Hacker NewsIran-Linked Hackers Disrupt U.S. Critical Infrastructure by Targeting Internet-Exposed PLCs
Iran-affiliated cyber actors are targeting internet-facing operational technology (OT) devices across critical infrastructures in the U.S., including programmable logic controllers (PLCs), cybersecurity and intelligence agencies warned Tuesday. "These attacks have led to diminished PLC functionality
 Dark Reading
Dark ReadingStorm-1175 Deploys Medusa Ransomware at 'High Velocity'
Microsoft says the financially motivated cybercrime group has exploited N-day and zero-day vulnerabilities in campaigns predicated on speed.
 Dark Reading
Dark ReadingGrafana Patches AI Bug That Could Have Leaked User Data
By hiding malicious instructions on an attacker-controlled Web page, AI could ingest orders that appear benign but return sensitive data to the attacker's server.
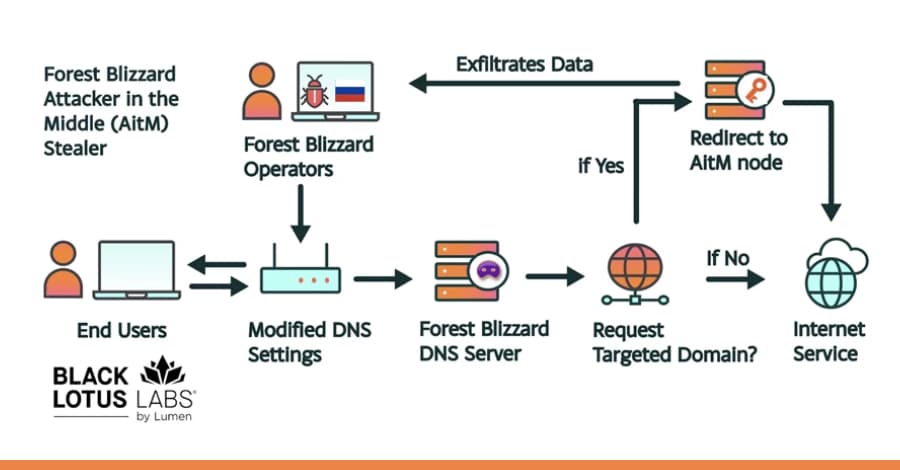
Russia Hacked Routers to Steal Microsoft Office Tokens
Hackers linked to Russia's military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon authentication tokens fr
 The Hacker News
The Hacker NewsRussian State-Linked APT28 Exploits SOHO Routers in Global DNS Hijacking Campaign
The Russia-linked threat actor known as APT28 (aka Forest Blizzard) has been linked to a new campaign that has compromised insecure MikroTik and TP-Link routers and modified their settings to turn them into malicious infrastructure under their control as part of a cyber espionage campaign since at l
![[Webinar] How to Close Identity Gaps in 2026 Before AI Exploits Enterprise Risk](/_next/image?url=https%3A%2F%2Fblogger.googleusercontent.com%2Fimg%2Fb%2FR29vZ2xl%2FAVvXsEgRHgJL0SczODx5PAnF85b8b0mRpiOOkIQdOWvhivyXu6H8UeZKH9ZUdaeW5IuU59q2hjMNioQWQ5vk1Km8yinGGc8GA079qvhTtFsp9PV76Kmp-3lpKh2zi3vgd_-6dFcOI6i1YHs7VkJ-p-HvOEuOwkjooBVSvYFOrVqXqNhZShZy3IUeD6BVHVvUIj50%2Fs1600%2Fwebinar-cerby.jpg&w=3840&q=75) The Hacker News
The Hacker News[Webinar] How to Close Identity Gaps in 2026 Before AI Exploits Enterprise Risk
In the rapid evolution of the 2026 threat landscape, a frustrating paradox has emerged for CISOs and security leaders: Identity programs are maturing, yet the risk is actually increasing. According to new research from the Ponemon Institute, hundreds of applications within the typical enterprise rem
 The Hacker News
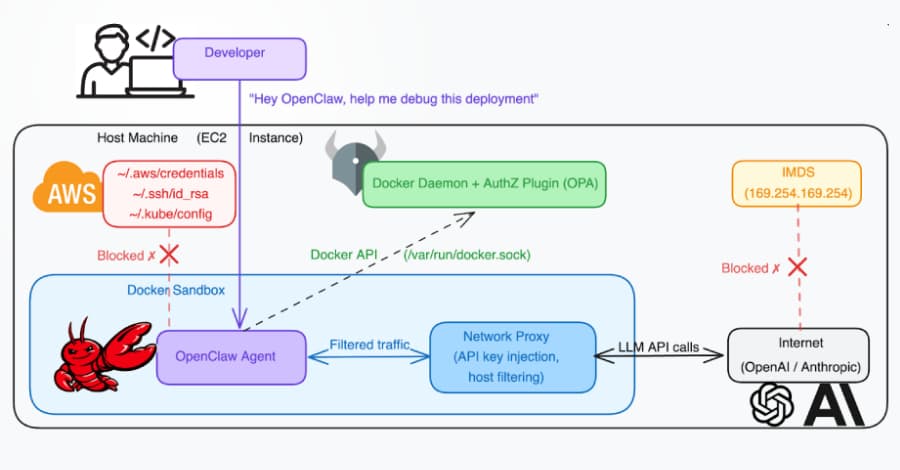
The Hacker NewsDocker CVE-2026-34040 Lets Attackers Bypass Authorization and Gain Host Access
A high-severity security vulnerability has been disclosed in Docker Engine that could permit an attacker to bypass authorization plugins (AuthZ) under specific circumstances. The vulnerability, tracked as CVE-2026-34040 (CVSS score: 8.8), stems from an incomplete fix for CVE-2024-41110, a maximum-se
 Dark Reading
Dark ReadingRSAC 2026: How AI Is Reshaping Cybersecurity Faster Than Ever
Dark Reading's Kelly Jackson Higgins shares insights on the past, present, and future of cybersecurity after attending RSAC 2026 Conference.
 Dark Reading
Dark ReadingHuman vs AI: Debates Shape RSAC 2026 Cybersecurity Trends
As AI dominated RSAC 2026, CISOs and industry leaders debated its role in security, from agentic applications to the challenges of scaling human involvement in decision-making.
 Dark Reading
Dark ReadingLies, Damned Lies, and Cybersecurity Metrics
A panel of five C-suite leaders discuss how cybersecurity success is measured and why it isn't improving results.
 Dark Reading
Dark ReadingFocusing on the People in Cybersecurity at RSAC 2026 Conference
AI dominated RSAC 2026 Conference, but it's still the humans in cybersecurity who matter most.
 The Hacker News
The Hacker NewsOver 1,000 Exposed ComfyUI Instances Targeted in Cryptomining Botnet Campaign
An active campaign has been observed targeting internet-exposed instances running ComfyUI, a popular stable diffusion platform, to enlist them into a cryptocurrency mining and proxy botnet. "A purpose-built Python scanner continuously sweeps major cloud IP ranges for vulnerable targets, automaticall
 The Hacker News
The Hacker NewsThe Hidden Cost of Recurring Credential Incidents
When talking about credential security, the focus usually lands on breach prevention. This makes sense when IBM’s 2025 Cost of a Data Breach Report puts the average cost of a breach at $4.4 million. Avoiding even one major incident is enough to justify most security investments, but that headline fi
 The Hacker News
The Hacker NewsNew GPUBreach Attack Enables Full CPU Privilege Escalation via GDDR6 Bit-Flips
New academic research has identified multiple RowHammer attacks against high-performance graphics processing units (GPUs) that could be exploited to escalate privileges and, in some cases, even take full control of a host. The efforts have been codenamed GPUBreach, GDDRHammer, and GeForge. GPUBreach
 The Hacker News
The Hacker NewsChina-Linked Storm-1175 Exploits Zero-Days to Rapidly Deploy Medusa Ransomware
A China-based threat actor known for deploying Medusa ransomware has been linked to the weaponization of a combination of zero-day and N-day vulnerabilities to orchestrate "high-velocity" attacks and break into susceptible internet-facing systems. "The threat actor's high operational tempo and profi